Security Design: Interpretation of Raysync File Transfer Acceleration Technology
November 24, 2020
With the explosive growth of data, the file transfer acceleration software was born. However, how to ensure the security of file transfer? How to ensure the security of transnational transfer?
In view of the above problems, we will analyze Raysync's six important security settings in this article, hoping to help more enterprises better identify the file transfer acceleration software.
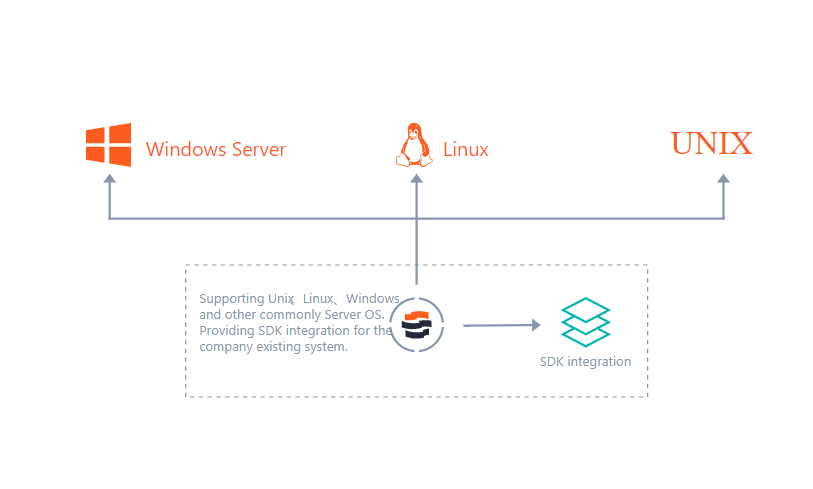
The following is the diagram of Raysync system architecture:

From the system architecture diagram, it can be seen that the file transfer acceleration process of Raysync software is not complicated, mainly based on the self-developed Raysync high-speed transfer protocol, which realizes the file transfer acceleration.
Will safety design be so simple? In fact, security is a topic that enterprise data assets always pay attention to. In the security design, every step of the user's operation and every click may bury potential safety hazards. The Raysync has been designed safely from six aspects:
Web security design
Account & password protection security design
Transfer security design
Software installation & operation security design
Behavioral audit
Encryption certificate life cycle management
You might also like

Industry news
July 31, 2020Enterprises are growing, and they want to move data flexibly and quickly anywhere, from server to server, from environmental testing to quality assurance, from one data center to another.
Industry news
August 3, 2020Many of our enterprise customers are migrating from complex file transfer solutions that require time-consuming configuration to Raysync.

Industry news
July 22, 2020Nowadays, the software development of technology and electronics companies requires frequent exchange and cooperation between on-site teams and off-site teams on source code.